Do you want to speed up your response to cyber attacks?
Do you know how cyber threats are impacting your company’s business?
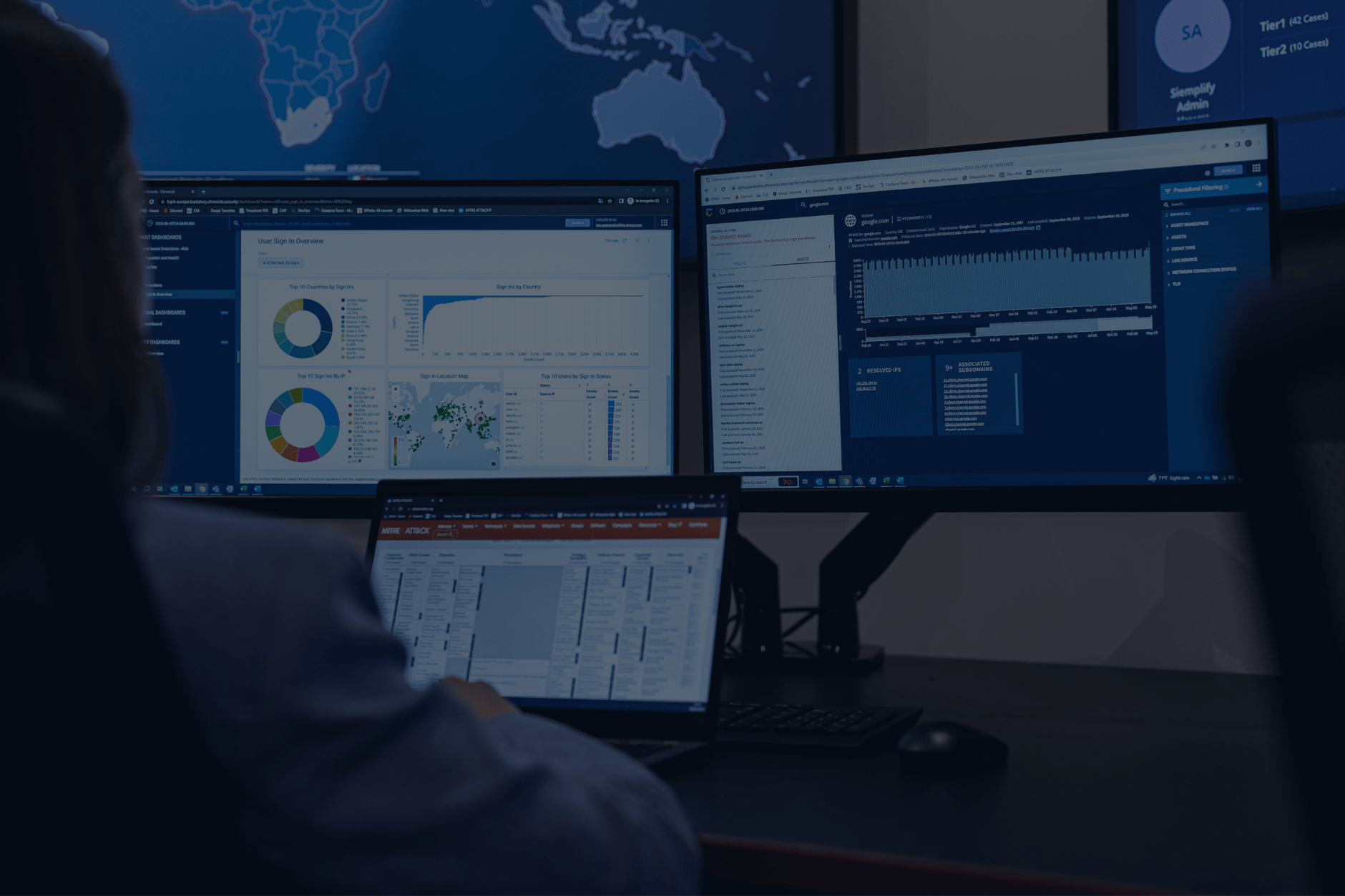
Whereas a typical SOC relies on time-consuming human analysis, the Re@ck Security Center combines BIP CyberSec’s DNA with Google Cloud technology to reduce Customers overload on investigation and information collection, and it implements a detection rule catalogue defined according to Customer’s actual cyber risks.
OUR APPROACH

After a decade of security advising organisations which operate in all the main sectors, we are facing a change in the top management’s perception of cybersecurity threats. We know how to effectively mitigate cybersecurity risks, so we wondered how we can respond to these new expectations.
KEY FEATURES
Transform your Security Operations team’s potential by unleashing the power of your people, processes, and technologies to drive unparallel influence throughout your organization.
KEY SERVICES AT A GLANCE
Get ready to elevate your team with BIP CyberSec top-notch managed services.
Monitor & Detect
Constantly monitor security events and promptly detect anomalies and security incidents
- Log Monitoring
- Event Detection
- Security Triage
Respond
Improve protection capabilities from attacks and threats, enhancing the security level of company assets
- Security Alerting
- Incident Escalation
- Incident Response
Threat Management
Adapt to dynamic environments and change security monitoring strategy according to new threats, vulnerabilities and risks
- Early Warning
- IoC Integration
- Retrospective Analysis
Security Management
Maximize detection on «known» attacks and minimize the “noise” generated by false positives
- Detection Rules management
- Playbook Management
- Security Device Management
Service Governance
Provide security operation trends and results to main stakeholders and constantly monitor the overall company risk exposure
- Top Management and Technical Reporting
- SLA Monitoring
- Service Review Meetings
- Continuous Improvement
Value-added Services
The Re@ck Security Center can include other BIP CyberSec services to provide an end-to-end Security Operation Center
- War Room Management
- Digital Forensics
- Intelligence Services:
- VIP Monitoring
- Data and Credential Leak Monitoring
- Anti-phishing
- Brand Monitoring
THE ARCHITECTURE
BIP Re@ck Security Center’s architecture is based on three core modules (Management, Intelligence & Monitoring Engines) which guarantee best-in-class technology stack and BIP CyberSec cybersecurity expertise.
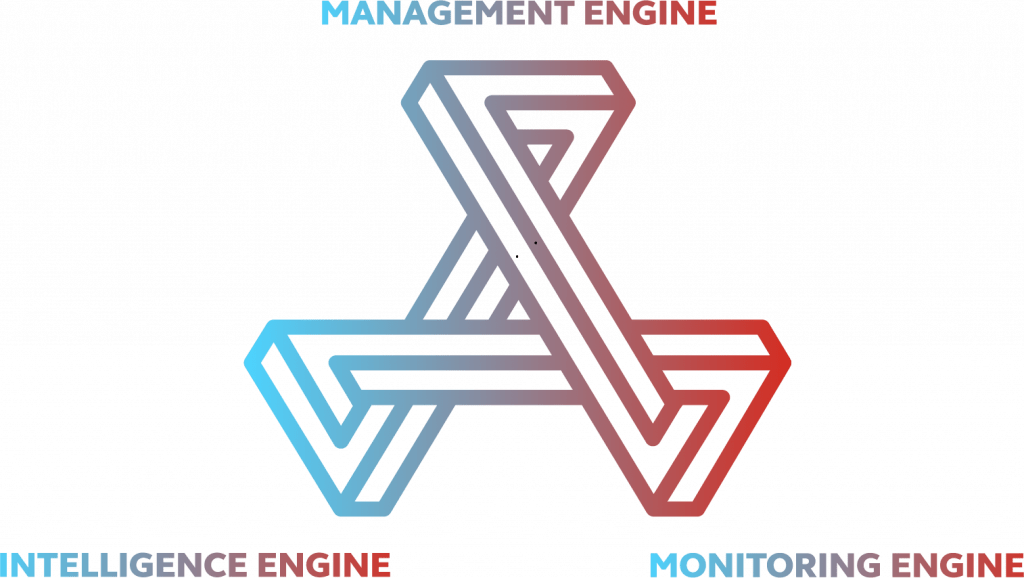
MANAGEMENT STATION
- Playbook management
- API management
- Vulnerability management
- Authentication & Authorization

INTELLIGENCE STATION
- Early Warning
- Threat Intelligence & IoC
- Threat Hunting

MONITORING STATION
- Chronicle SIEM
- Chronicle SOAR
- Ticketing systems
- Reporting, dashboard and KPI
GOOGLE CHRONICLE SIEM & SOAR
- Wide range of supported device types and vendors, including multi-vendor cloud-based environment
- Planet-scale distributed system for storing and analyzing all enterprise security telemetry
- At fixed price (per users, not based on volume of data ingested)
- Detection in real-time at Google speed, on entire telemetry till 12 months of online events
- Rich, extensible Unified Data Model for event taxonomy, including Asset and User
- Data correlation across common entities to analyze telemetry faster
- IoC integration to drive efficiencies and to enable faster search
- Correlate different security events into one unique security incident using machine learning and artificial intelligence
- Minimize time to respond
- Minimize Customer effort in managing SOC outcome
- Easily apply playbook to automatically respond to incident
- Interaction with other source to enrich the analysis and engage impacted owners through trouble ticketing systems
- Free resources for “unknown” research (Threat Hunting)
Are you interested?
Get in touch with our specialists to catch our Re@ck Security Center in action!
Get in touch with our specialists to catch our Re@ck Security Center in action!

© 2022 – Business Integration Partners S.p.A. | CyberSec Practice – VAT: 03976470967
Headquarters
Torre Liberty Building
Galleria de Cristoforis 1, Milan, 20121
Italy
Registered Office
San Babila
Piazza San Babila 5, Milan, 20122
Italy