Ransomware attacks keep raising due to their profitability. How can a company protect itself from these attacks?
What is Ransomware?
Ransomware is a form of malware designed and developed to encrypt files on devices, rendering them, along with the systems that use them, unusable.
The goals of ransomware and malicious actors who employ them are multiple: what they have in common is that they heavily disrupt business processes and critical services, and demand a ransom payment in exchange for the private key needed to decrypt the data targeted by the attack.
In recent years, ransomware attacks have surged, increasingly targeting government entities and critical infrastructure. Similarly, the technologies of the attacks themselves and malicious actors’ skills have advanced significantly, bringing the impact of this type of attack to new heights, including the propagation of ransomware “infections” over entire networks, and the ||deletion of recovery and backup systems.
To address the risk of ransomware, as well as organize an effective and efficient response to incidents it causes, the most authoritative organizations and communities in the sector have drawn up a series of guidelines and best practices.
Let’s explore the best practices for avoiding ransomware attacks and securing your business.
Avoid being an easy target for Ransomware
Ransomware attacks have evolved over the years. Attackers nowadays are structured as small businesses which search, attack and ransom systematically by following an easy-to-kill strategy which maximizes their return of investment. A group like Lockbit has This can be achieved by leveraging 2 factors:
- Attack Complexity (AC): increasing the overall cost for an attack to be successful.
- Mean Time To Detect (MTTD): increasing the opportunity for the blue team to detect an ongoing attack before it reaches its objective.
“Increasing attack complexity” can be directly translated to “Increase costs for threat actors” and will be analysed in the following paragraph.
Decreasing MTTD can drastically reduce the impact of an attack, detecting indicators of compromise (IOCs) that will initiate the investigation and response of the threat.
Prevent malicious attacks: the assumed breach mindset
 Due to the well-tested monetisation scheme adopted by ransomware groups, these types of malicious attack are expected to continue rising. The advised strategy is to operate under the assumed breach mindset. This is advised even for organisations that focus on a strong hardening of their external perimeter, as attackers work with hackers specialised in initial access (Initial Access Brokers) and may use paid insiders.
Due to the well-tested monetisation scheme adopted by ransomware groups, these types of malicious attack are expected to continue rising. The advised strategy is to operate under the assumed breach mindset. This is advised even for organisations that focus on a strong hardening of their external perimeter, as attackers work with hackers specialised in initial access (Initial Access Brokers) and may use paid insiders.
The best practices for implementing an assumed breach mindset are:
Threat Model
An organisation should have a clear threat model and be aware of the current threat landscape to choose the right strategy and controls to mitigate and reduce its exposure to risk. It is also important to keep up-to date with the challenges posed by new technologies and in ever changing ways of working (such as remote working). Without a threat model, an organisation cannot know its weak points, and cannot make improvements in the areas where they are needed. A common issue with remote working is to rely on strong authentication using 2FA, but with poor “posture checks”, allowing unmanaged devices to access company’s resources remotely (e.g. via VPN) and access online services such as Microsoft 365 without any restriction.
Secure
The company should leverage the People-Process-Technology framework in order to increase its resilience: to mitigate most threats, all three dimensions are needed. The most effective measures most organizations should evaluate include:
- People: Awareness training for employees, focused on phishing/vishing and MFA fatigue. Hiring of an internal blue team and recurring training. Understanding the way business works in the specific context, focusing on establishing a baseline to detect any later deviation from the .
- Process: Definitions of plans to prevent and respond to the various threats identified by threat modelling. Train people to follow the tasks and duties reported in those processes, recognizing any point-of-failure in advance.
- Technology: Adopt a minimal set of technological countermeasures that maximize the return on investment (such as EDR, CASB, MFA, …) and tune them to fit the context and business needs. Later, evaluate additional safeguards (such as MDM, IDS, …)
Test
Once the security measures are in place they must be tested to evaluate their effectiveness. There are multiple ways to test an organisation’s security measures; common methods include:
- People
- Do employees fall victim to phishing emails?
- Do employees authorize unsolicited MFA notifications? (https://tech.co/news/mfa-fatigue-hackers)
- Process
- Are systems up-to-date with the latest patches?
- How long does it take to get the owner of an asset by its IP address?
- Technology
- Are events (ex. Login fail) on cloud collected?
- Complex
- What happens if ransomware infects a company laptop?
- Is it possible for an attacker to physically enter the offices and connect to the internal network?
In our experience with clients in many sectors, security solutions are often deployed without proper testing. One of the most common issues we find is the failure to determine a user’s IP in the internal network when connecting via VPN, a key requirement for incident response.
Ransomware attacks Simulation
In recent years, Bip CyberSec has consistently focused on giving the best answer to the question “What happens if ransomware infectes a company laptop?”.
Our solution is a Ransomware Simulation Service, a subset of our Breach and Attack Simulation service focusing on the simulation of a specific threat.
Only with a comprehensive simulation is it possible to evaluate all the risks and impacts of attack in a specific environment, due both to the complexity of such attacks, and to the constant escalation in attack tactics, techniques and procedures, which are developed on a daily basis.
Ransomware Simulation allows the organisation to evaluate the effectiveness of its security controls and to measure the impact of ransomware in a controlled and secure environment before the real attack occurs.
Defending against Ransomware with Bip CyberSec
Defending against ransomware is not easy. Adversaries’ tactics evolve continuously: attack surfaces are generally expanding as services and technologies evolve, and social engineering always finds ways to bypass security measures (even MFA).
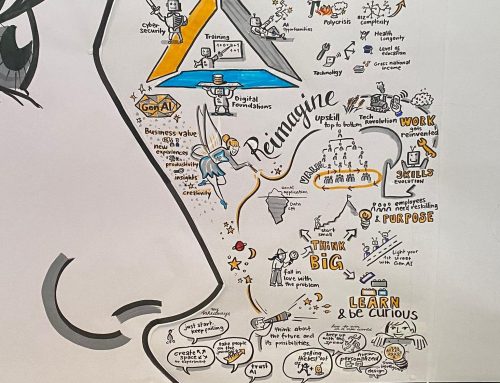
Our approach, aligned with industry best practice, can be summarised as:
Learn more about how we work with it here, and contact us to get a simulation with our experts.